Flashpoint Vulnerability Intelligence has surpassed cataloging 7,000 known exploited vulnerabilities, surpassing another major milestone as vulnerability disclosures accelerate across the global attack surface.
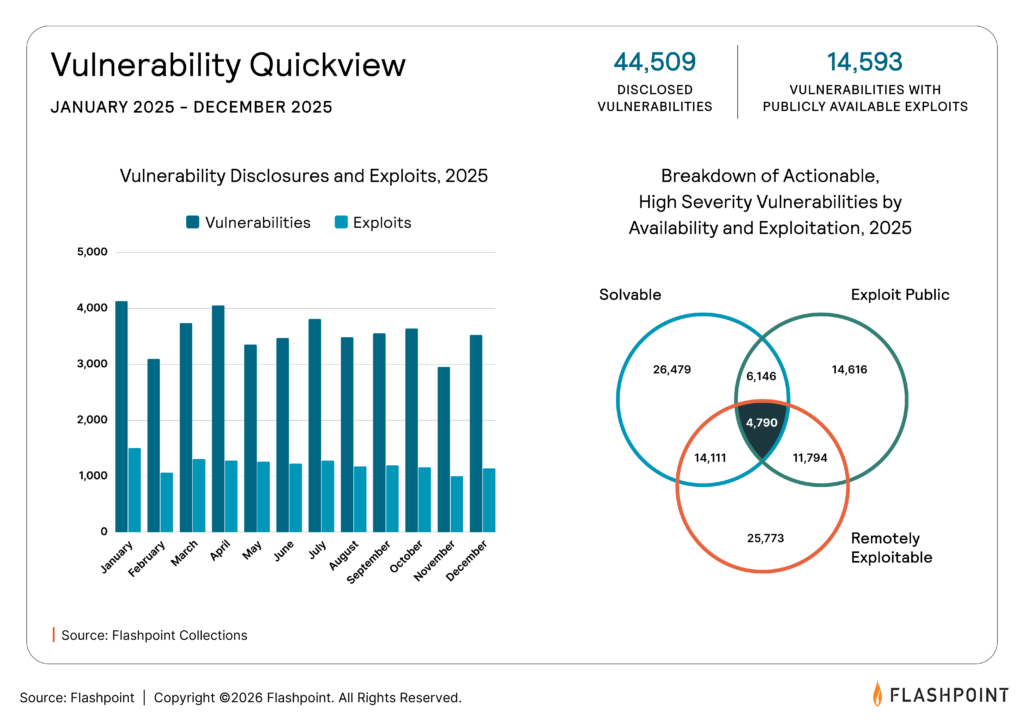
In 2025, Flashpoint tracked 44,509 disclosed vulnerabilities, a pace that continues to accelerate into 2026. Of those, 14,593 had publicly available exploits (1,944 more with proof-of-concepts), giving threat actors immediate pathways to weaponization.
This pace is shaping how exploitation unfolds, with high-impact vulnerabilities being operationalized within hours or days, particularly when they affect widely deployed technologies or core infrastructure.
Security teams are operating within this compressed environment every day. They are reviewing more findings across open-source software, commercial applications, cloud environments, and third-party dependencies, while working within tighter timelines to assess impact and take action.
Flashpoint’s latest milestone of surpassing 7,000 known exploited vulnerabilities (KEVs) cataloged reflects that reality. It highlights how vulnerability management programs are evolving toward prioritization as a core capability, with a focus on vulnerabilities tied to active exploitation and real-world risk.
What The 7,000+ KEV Milestone Means for You
Security teams are operating in a high-volume environment. Vulnerabilities are disclosed continuously across open-source software, commercial applications, cloud environments, and third-party dependencies. At the same time, advancements in automation and code analysis are increasing the rate at which new findings are surfaced.
Each of these findings enters an already crowded workflow. Teams are expected to determine relevance, urgency, and impact quickly, often with limited context. This is where risk-based decision making becomes essential.
Flashpoint tracks hundreds of thousands of vulnerabilities across thousands of sources. Within that dataset, a much smaller percentage shows confirmed exploitation activity. That concentration of risk informs how effective programs allocate time and resources.
Crossing the 7,000+ KEV milestone goes beyond scale to provide greater precision, deeper context, and stronger confidence in how teams prioritize and act on the most critical vulnerabilities.
- Validated threats: Each KEV entry reflects observed exploitation in the wild by threat actors, including APT groups, cybercriminal operations, ransomware presence, and automated botnets.
- Exploit-aware prioritization: In reality, only a small percentage of tracked vulnerabilities drive real-world incidents. FP KEV provides visibility into that subset so teams can focus remediation efforts where they have immediate impact.
- Human-curated intelligence: Every entry is reviewed, validated, and enriched by analysts, with context on exploit maturity, adversary usage, and remediation pathways when available.
This level of clarity allows teams to move faster without sacrificing accuracy. It supports vulnerability management programs that are built around real-world attacker behavior and aligned to current risk.
How Public Vulnerability Data Fits Into the Picture
Public vulnerability catalogs remain useful reference points for tracking disclosures and confirmed exploitation. The CISA Known Exploited Vulnerabilities catalog, for example, gives security teams a curated view into a limited set of vulnerabilities that have been exploited in the wild that impact U.S. government stakeholders.
For many organizations, though, that level of visibility is not enough.
Public catalogs capture only part of the picture. They tend to reflect a narrower slice of exploitation activity, with less detail on how vulnerabilities are being used, which actors are leveraging them, and what defenders should do next. They also rely heavily on CVE-based tracking, leaving gaps around non-CVE exposures and other vulnerabilities that still carry operational risk.
Flashpoint’s FP KEV and Vulnerability Intelligence provide a broader and more actionable view. The advantage is visible in both scale and depth. Of the 7,000 known exploited vulnerabilities in FP KEV, over 800 are missing from CVE. That expanded coverage is paired with the context security teams need to prioritize effectively, including exploit maturity, adversary mapping, affected product detail, and remediation guidance.
| Dimension | Public KEV Catalogs | Flashpoint FP KEV |
| Scope | Varies by provider, with coverage dependent on available sources and methodology | Global, cross-industry coverage |
| Coverage | CVE-based tracking | CVE and non-CVE vulnerabilities |
| Context | Limited enrichment | Exploit maturity, adversary mapping, remediation |
| Update Model | Periodic updates | Continuously updated with analyst input |
This is what separates a reference list from an operational dataset. Teams need vulnerability intelligence that supports triage, remediation, reporting, and broader risk reduction efforts. Wider visibility and deeper context make that possible.
The Critical Role of Human-Curated Intelligence
Vulnerability data originates from a wide range of sources with varying levels of completeness and accuracy.
Flashpoint’s intelligence model includes analyst validation to ensure consistency and depth across the dataset.
This process includes:
- Reviewing disclosures across public and private sources
- Validating exploit availability and usage
- Enriching entries with technical and operational context
Analyst input supports:
- Accurate classification of vulnerabilities
- Clear understanding of exploitation pathways
- Timely updates as activity evolves
Supporting Decision-Making Across Teams
Vulnerability intelligence feeds multiple functions across an organization. Teams use this data to align technical actions with current threat activity.
Common use cases include:
- Vulnerability management: Align patching priorities with active exploitation trends.
- Threat intelligence: Map vulnerabilities to threat actor campaigns and observed behaviors.
- Security operations: Tune detection based on known exploit techniques.
- Executive reporting: Communicate risk posture using data tied to real-world activity.
Each of these functions relies on consistent, enriched intelligence to maintain alignment.
Proactively Address Vulnerability Risk
Vulnerability discovery continues to expand across software ecosystems, infrastructure, and identity layers.
Security teams require a clear understanding of which issues are relevant to their environment at any given time.
Flashpoint provides primary source intelligence that supports this need through:
- Continuous monitoring of vulnerability disclosures and exploitation
- Analyst-driven validation and enrichment
- Integration-ready data for operational workflows
This approach enables teams to maintain focus, allocate resources effectively, and respond to risk based on current threat activity. Request a demo and learn more today.


