flashpoint ignite » managed attribution
Flashpoint Managed Attribution
Connect threat intelligence to live research and analysis with a fully managed isolated environment built for every stage of the investigation.
How Teams Use Flashpoint Managed Attribution
Primary Source Research
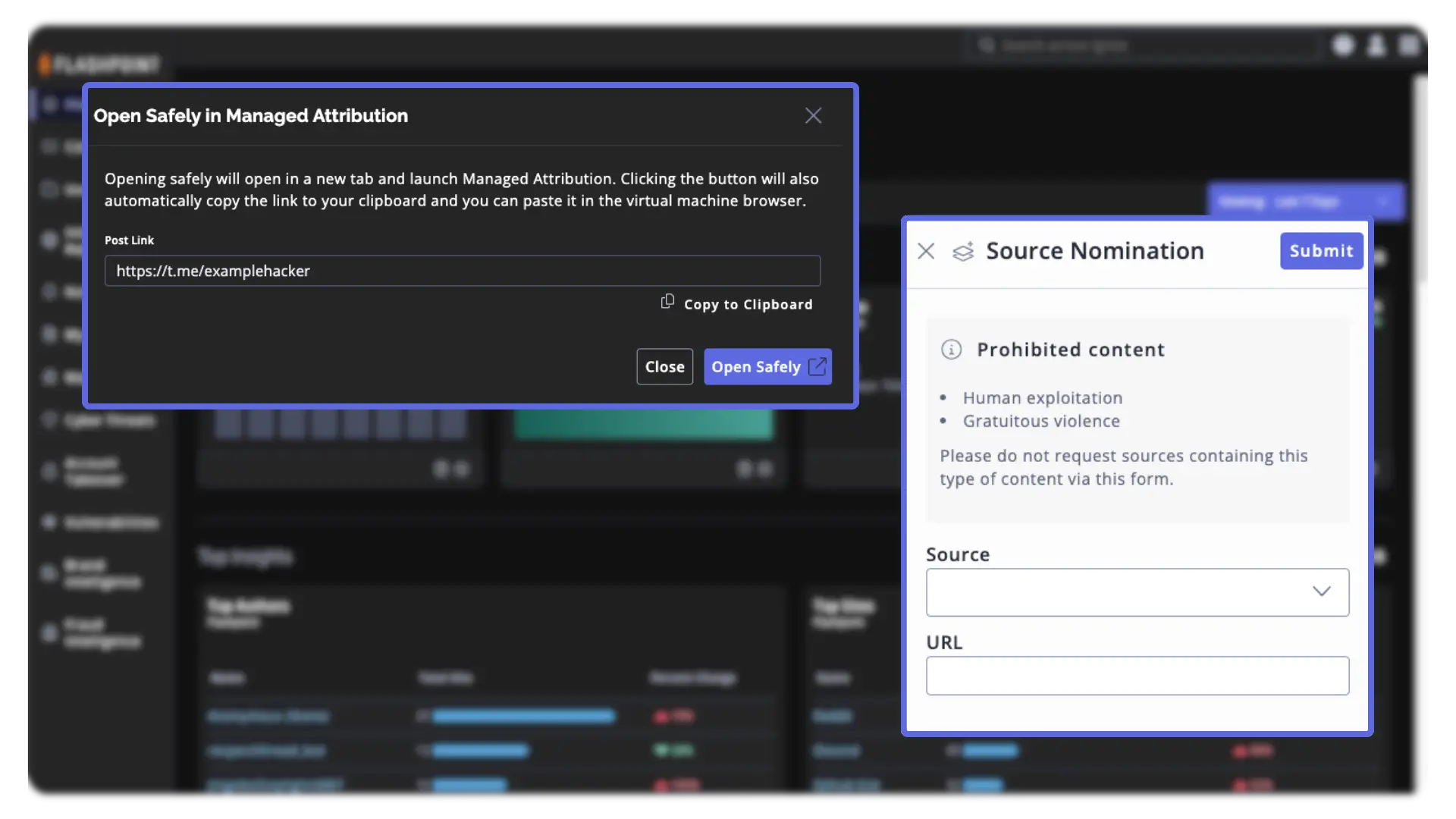
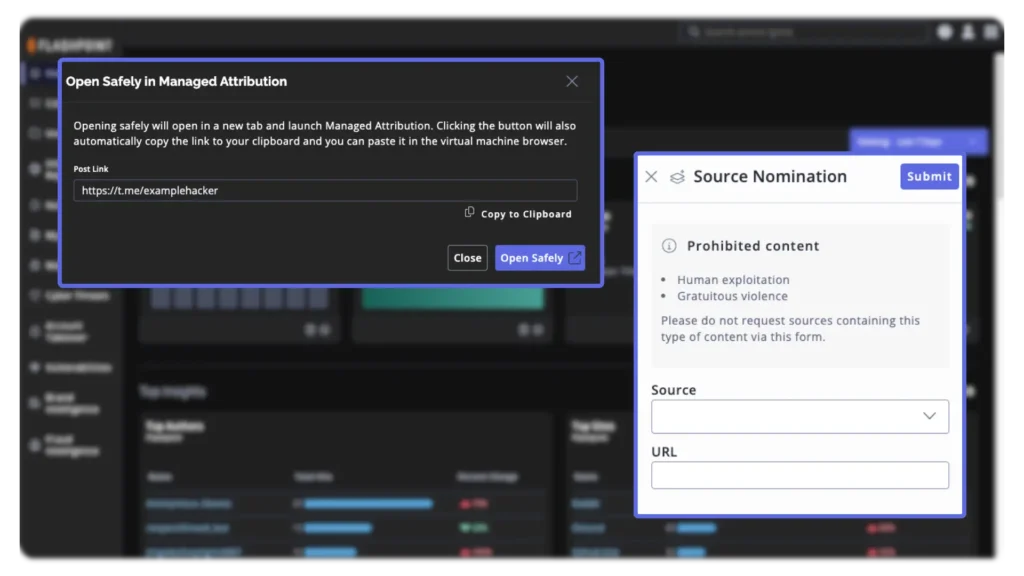
Safely pursue investigations beyond the boundaries of threat intelligence platforms, pivoting from Flashpoint Ignite to an anonymous browser or full virtual machine to investigate content at its source.
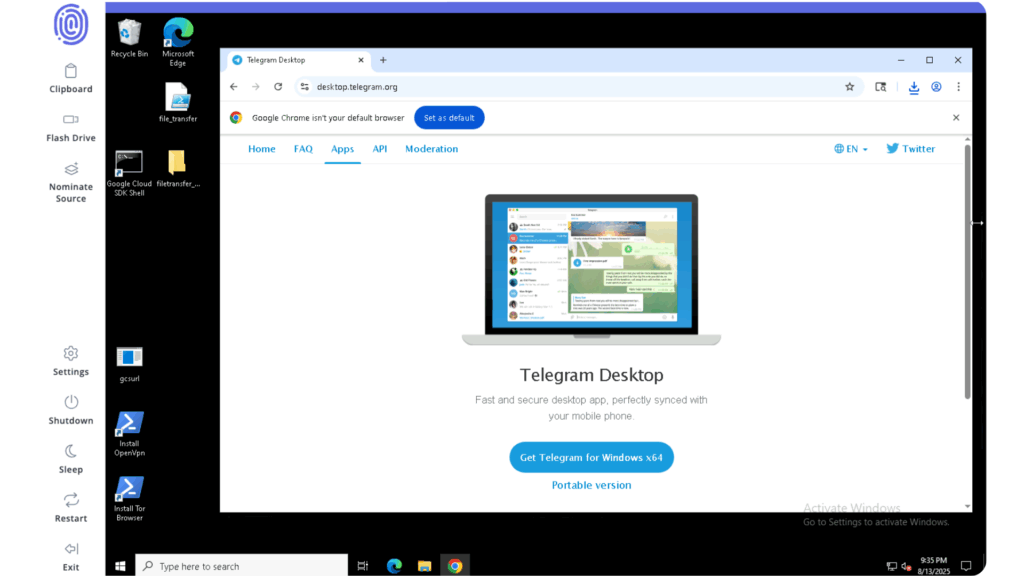
Threat Actor Engagement
Anonymously engage with threat actors in online communities, obfuscating traceable information and ensuring the destruction of virtual environments on demand.
Technical Investigations
Respond quickly to targeted attacks by deploying any program required, such as OSINT applications and reconnaissance tools, to safely investigate the full extent of a threat.
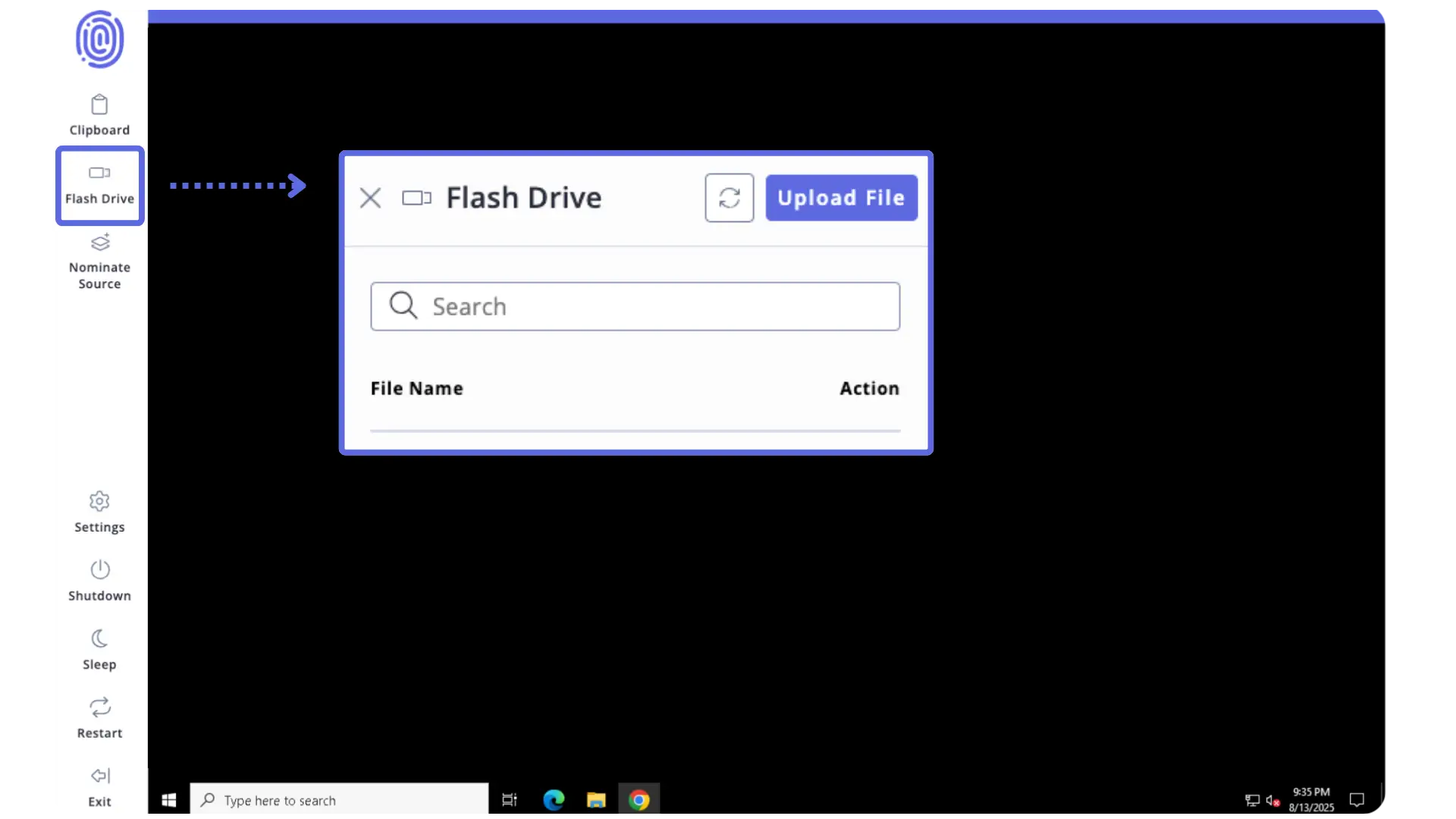
Secure Data Access
Safely navigate to breach websites and ransomware blogs, download data into a virtual environment, assess the extent of the damage, and take decisive action in the event of a data breach.
The Intelligence Difference:
Flashpoint vs. The Status Quo
Status Quo
❌ Self-hosted Virtual Machines (VMs) require maintaining independent hardware, software, and compliance, demanding coordination across internal security, IT, and legal teams and diverting resources from core investigations.
❌ Analysts are often limited to browser-only research tools or hit dead ends when investigations require more. Standalone browsers cannot support the full spectrum of tools required by CTI and investigative teams.
❌ Analysts may rely on less secure methods like burner laptops, which are not scalable and are less secure than a cloud-hosted system. Configuring traffic routes creates the ongoing risk that threat actors may learn their location or identity.
❌ Researchers face serious risk when downloading files from potentially malicious websites such as breach sites, due to the threat of malware, trackers, or infection of the host system.
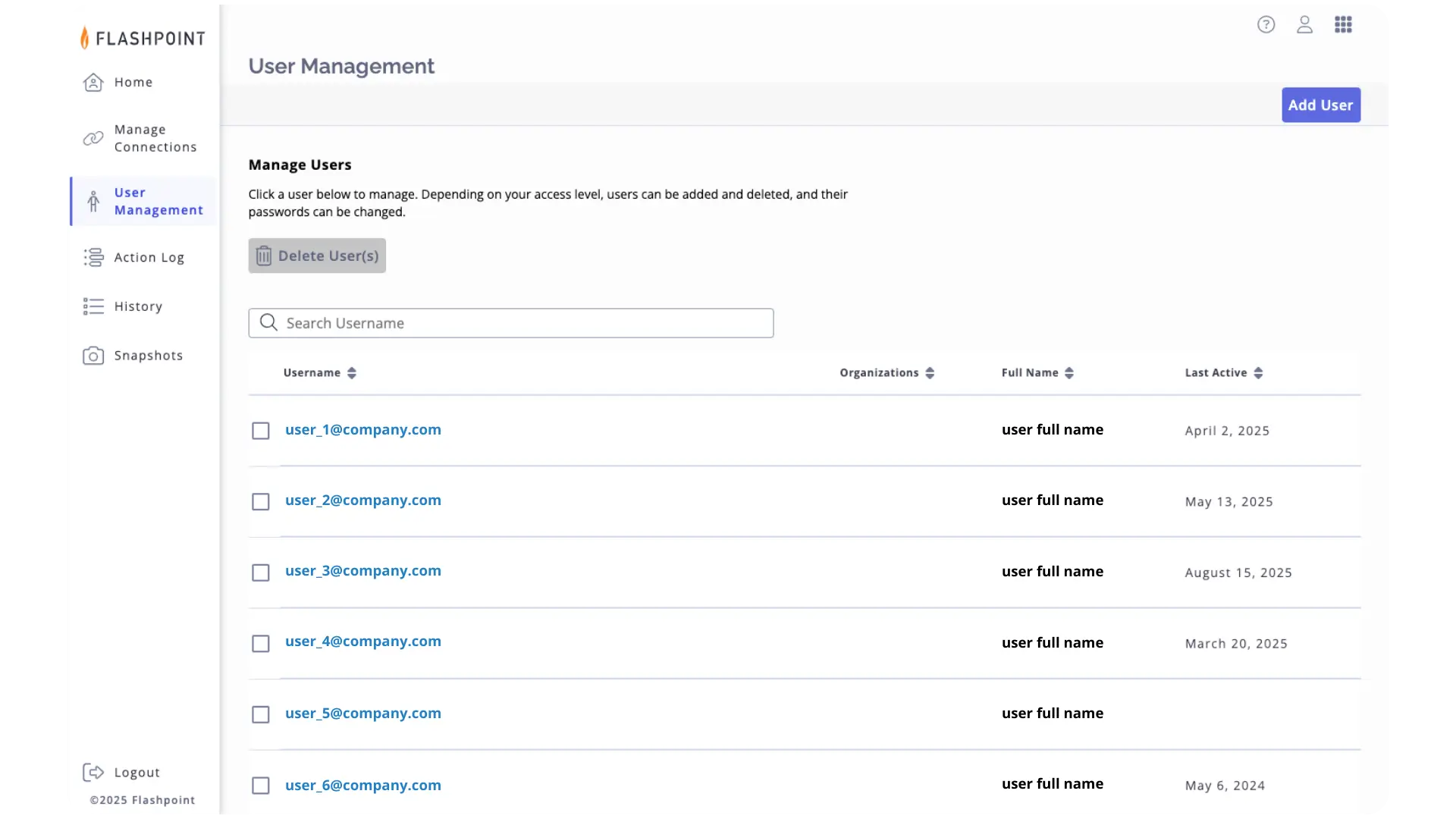
✅ Flashpoint Managed Attribution eliminates the need to build and maintain self-hosted VMs, allowing your team to focus entirely on the investigation, shifting infrastructure and maintenance to Flashpoint.
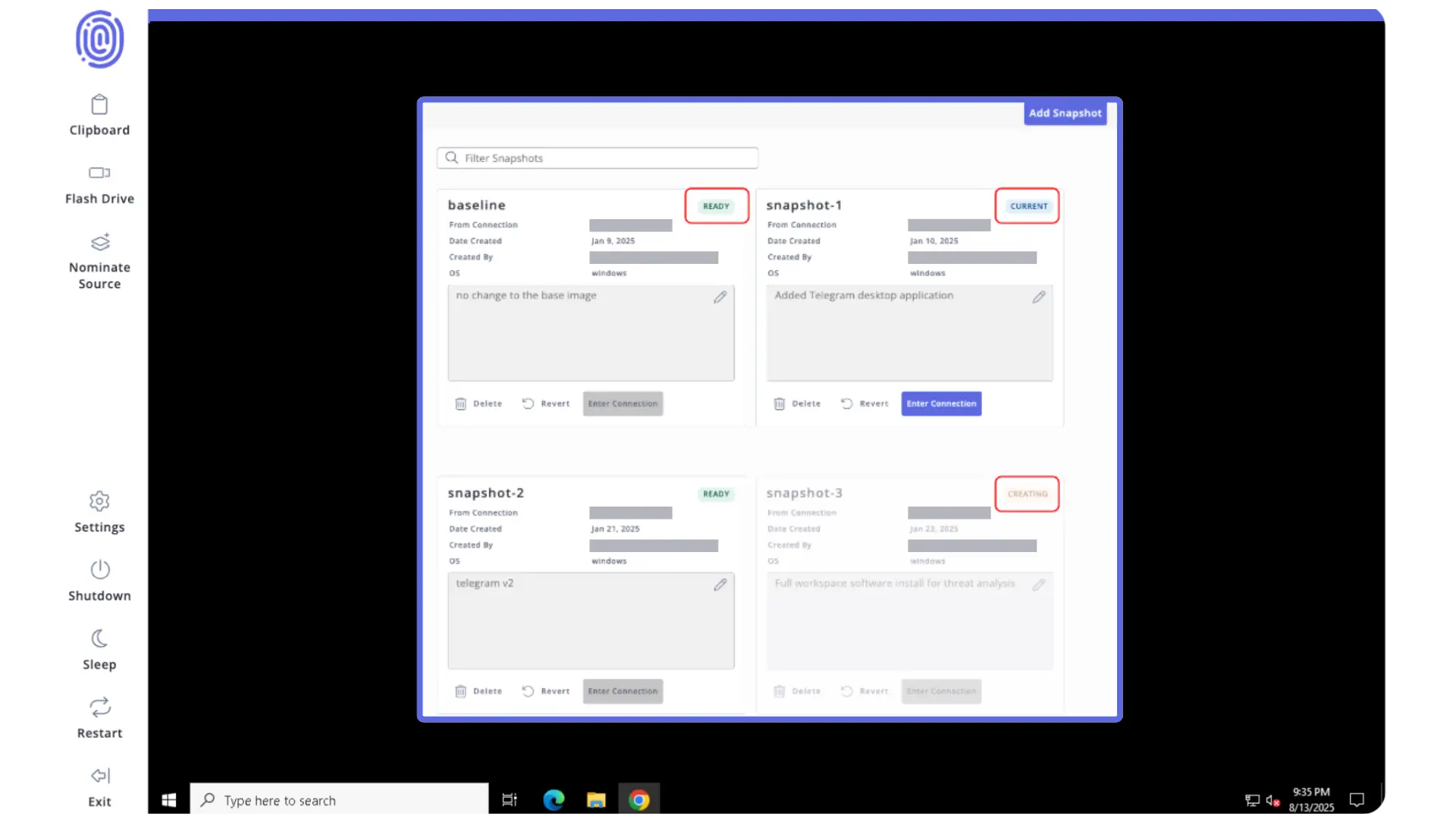
✅ Flashpoint Managed Attribution provides a complete virtual environment that goes beyond browser-only tools. Analysts can discover a potential threat in Flashpoint Ignite, rapidly triage in a lightweight, isolated browser, then transition to a persistent Managed VM for deeper analysis.
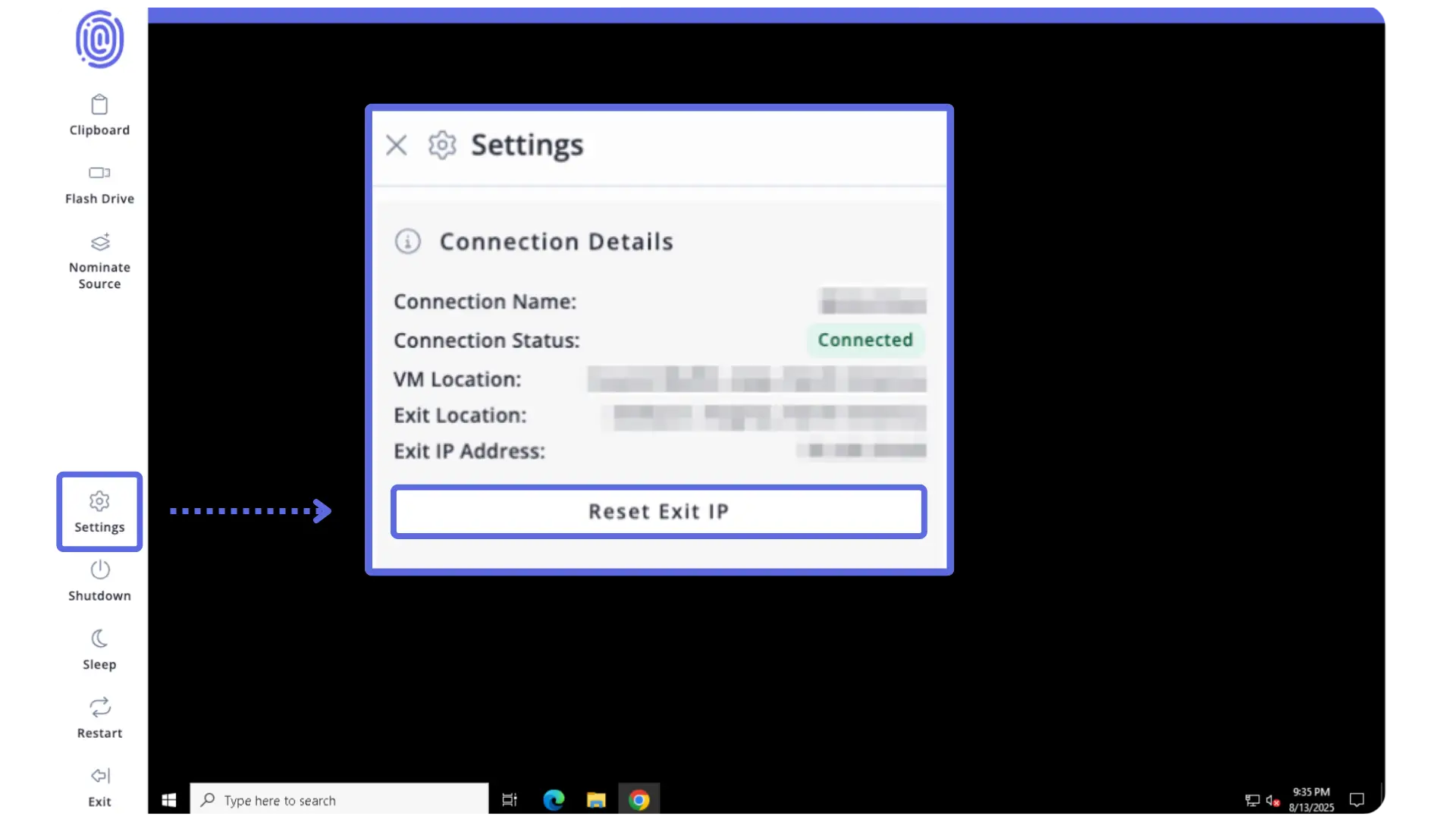
✅ Customers can choose from Points of Presence (POPs) in 40+ regions and configure multi-hop gateways for extra layers of obfuscation, ensuring digital activity cannot be traced back to the organization, computer, or personal information.
✅ Flashpoint Managed Attribution is a secure, isolated virtual environment. Users can safely upload, download, and transfer files, and destroy the virtual environment on demand to eliminate traceable information or malware.
The Intelligence Difference:
Flashpoint vs. The Status Quo
Status Quo
❌ Self-hosted Virtual Machines (VMs) require maintaining independent hardware, software, and compliance, demanding coordination across internal security, IT, and legal teams and diverting resources from core investigations.
❌ Analysts are often limited to browser-only research tools or hit dead ends when investigations require more. Standalone browsers cannot support the full spectrum of tools required by CTI and investigative teams.
❌ Analysts may rely on less secure methods like burner laptops, which are not scalable and are less secure than a cloud-hosted system. Configuring traffic routes creates the ongoing risk that threat actors may learn their location or identity.
❌ Researchers face serious risk when downloading files from potentially malicious websites such as breach sites, due to the threat of malware, trackers, or infection of the host system.
✅ Flashpoint Managed Attribution eliminates the need to build and maintain self-hosted VMs, allowing your team to focus entirely on the investigation, shifting infrastructure and maintenance to Flashpoint.
✅ Flashpoint Managed Attribution provides a complete virtual environment that goes beyond browser-only tools. Analysts can discover a potential threat in Flashpoint Ignite, rapidly triage in a lightweight, isolated browser, then transition to a persistent Managed VM for deeper analysis.
✅ Customers can choose from Points of Presence (POPs) in 40+ regions and configure multi-hop gateways for extra layers of obfuscation, ensuring digital activity cannot be traced back to the organization, computer, or personal information.
✅ Flashpoint Managed Attribution is a secure, isolated virtual environment. Users can safely upload, download, and transfer files, and destroy the virtual environment on demand to eliminate traceable information or malware.
What Flashpoint Managed Attribution Delivers
Ensure Continuous OpSec with Global Attribution Control
Focus entirely on the investigation, knowing your digital activity is anonymous and untraceable. Choose from points of presence (POPs) in 40+ regions and link additional gateways for extra layers of obfuscation, instantly changing your exit location or resetting your IP on demand.
Conduct Thorough Research with a Customizable Workspace
Flashpoint Managed Attribution is more than a browser. It’s a fully functional isolated workspace that allows you to install and run any programs your OSINT and technical investigations require, without being limited by a pre-built suite of tools.
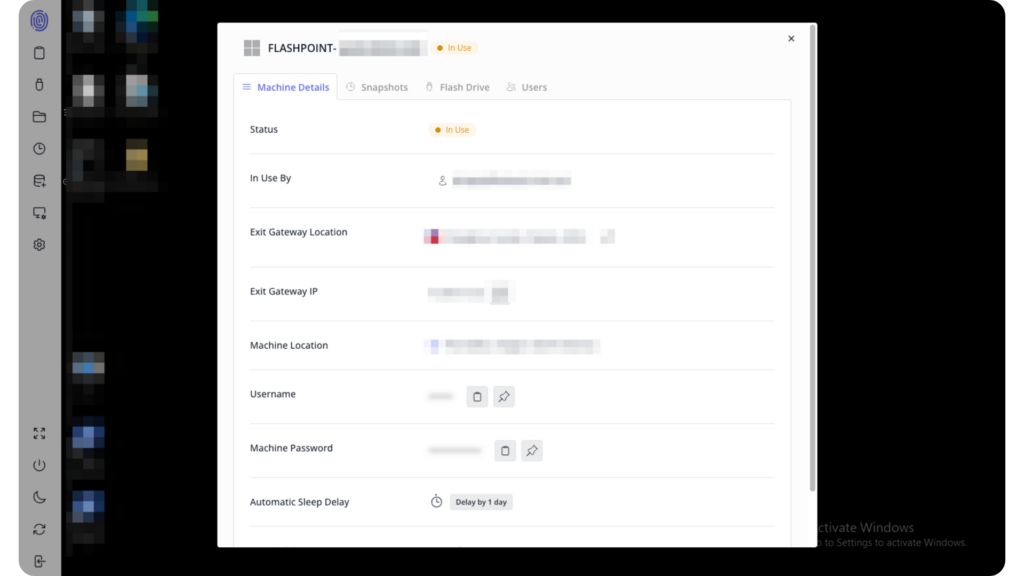
Eliminate the Operational Security Burden
No need to maintain independent hardware, software, and compliance for self-hosted VMs. Coordinating with internal security, IT, and legal teams adds burden and diverts critical time away from core tasks. Flashpoint handles this all for you, so your team can focus on investigations and analysis.
How does Flashpoint Managed Attribution compare to Authentic8 SILO?

Unlike SILO, which only provides a virtual browsing experience, Flashpoint Managed Attribution is a fully isolated virtual computer that allows you to download files, install programs, and conduct advanced digital operations securely. Learn more →
Additional Offerings
Complement Managed Attribution with Flashpoint Ignite
Pivot your investigations between Flashpoint Managed Attribution and Ignite to cover multiple layers of research. Discover a potential threat and instantly pivot to perform rapid triage in an isolated browser, then transition to a persistent Managed VM for deep analysis, all within the same ecosystem. Nominate new sources from within your Managed Attribution environment to keep Flashpoint collections in step with your investigations.
Add Managed Intelligence to Augment Your Team
Our expert analysts provide intelligence collection, analysis, and reporting, delivering tailored insights directly to you. This augments your internal resources, ensures comprehensive coverage, and frees your team to focus on critical, high-impact tasks.
“We see Flashpoint not just as a vendor, but as a trusted advisor helping us mature our threat intelligence program year over year.”
Head of Cyber Intelligence
Global Insurance Company