comparison
Flashpoint vs. A Leading Competitor
Threat vectors are converging – cyber and physical threats are overlapping and intersecting, including vulnerability exploits, compromised credentials, ransomware, malware, physical security threats, and other forms of cyberattacks.
As threat vectors converge, security and intelligence leaders across the public and private sectors should aim to unify and rally their security and intelligence teams behind a single source of truth that integrates workflows between their Cyber Threat Intelligence (CTI), Fraud, Vulnerability Management (VM), and Physical Security teams, as well as other functions.

How Flashpoint Stacks Up





Learn more about Flashpoint’s best-in-class intelligence and analysis
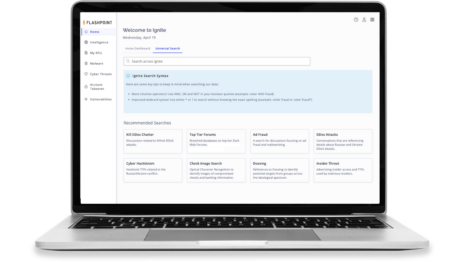
Flashpoint’s Ignite Platform brings together team-tailored intelligence across multiple groups into one workspace.
With a holistic view of risk in one place, security experts can finally close the gap between data, intelligence, and action.
Leverage timely, actionable intelligence
Our continuous data collections contain more than 2 petabytes of threat intelligence data, from ransomware group profiles to stolen accounts, credit cards, and credentials.
Identify, prioritize, and remediate
threats faster
With finished intelligence, exposure dashboards, asset-based vulnerability intelligence, and automation, you can easily identify, prioritize, and remediate risks quickly.
Partner with the experts in threat intelligence
Our 100+ analyst team engages with threat actors in illicit communities, provides tailored and custom information based on requests, and offers threat response and readiness to support all your needs.