Blog
Potential Link of Compromised Zoom Accounts to Previously Compromised Credentials
Flashpoint analysts are aware of recent claims that a few thousand compromised Zoom accounts have been made available on the Deep & Dark web. Flashpoint has obtained the referenced list of compromised Zoom accounts and we have processed the credentials in our Compromised Credentials Monitoring – Enterprise (CCM-E) system within our platform and impacted customers have been notified.

Flashpoint analysts are aware of recent claims that a few thousand compromised Zoom accounts have been made available on the Deep & Dark web. Flashpoint has obtained the referenced list of compromised Zoom accounts and we have processed the credentials in our Compromised Credentials Monitoring – Enterprise (CCM-E) system within our platform and impacted customers have been notified.
Flashpoint determined that the compromised credentials contained within this file were likely previously leaked credentials that had been tested and validated for password reuse on Zoom accounts using an unknown account checker tool with a “config” file designed specifically for Zoom.
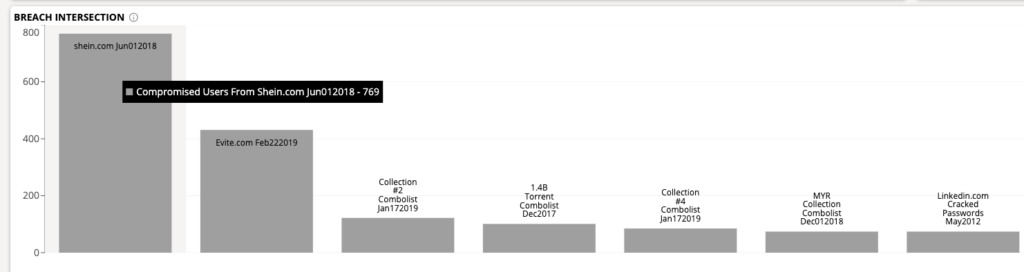
By leveraging the Flashpoint Intelligence Platform Breach Dashboard component of CCM-E, we can confirm that there is significant intersection with previously leaked breaches:
Flashpoint regularly observes threat actors selling or sharing output (validated credentials for Zoom accounts) from account checking tools within the illicit communities that we collect from, so this type of activity is normal to see and is expected to continue. Recently, given the massive increase in dependency upon technologies like Zoom, there has been a roughly ten-fold increase in conversations regarding Zoom account security or sales of Zoom accounts across our datasets:
Another interesting example is the increase in the number of Zoom accounts that can be found on Genesis Market, which has a direct correlation with the increased usage over the past several weeks. Flashpoint has observed a five-fold increase in accounts for sale over the past month, with the highest increases in the past two weeks.
Flashpoint analysts will continue to monitor for threats to Zoom, including compromised or leaked accounts. For continued coverage of threats related to COVID-19, please visit our blog here.

