Flashpoint’s VulnDB™️ documents over 400,000 vulnerabilities and has over 6,000 entries in Flashpoint’s KEV database, making it a critical resource as vulnerability exploitation rises. However, if your organization is relying solely on CVE data, you may be missing critical vulnerability metadata and insights that hinder timely remediation. That’s why we created this weekly series—where we surface and analyze the most high priority vulnerabilities security teams need to know about.
Key Vulnerabilities:
Week of December 20 – December 26, 2025
Foundational Prioritization
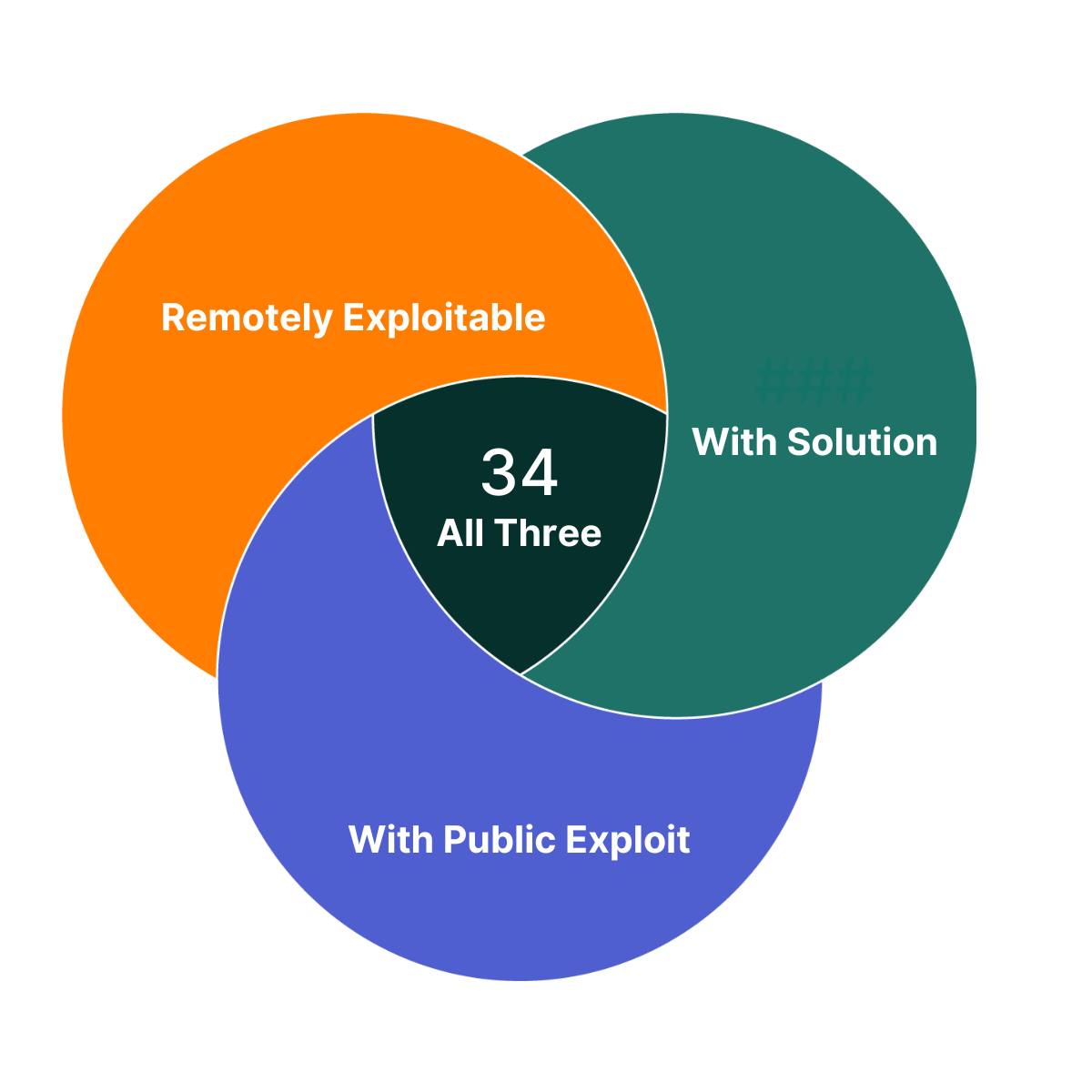
Of the vulnerabilities Flashpoint published this week, there are 34 that you can take immediate action on. They each have a solution, a public exploit exists, and are remotely exploitable. As such, these vulnerabilities are a great place to begin your prioritization efforts.
Diving Deeper – Urgent Vulnerabilities
Of the vulnerabilities Flashpoint published last week, four are highlighted in this week’s Vulnerability Insights and Prioritization Report because they contain one or more of the following criteria:
- Are in widely used products and are potentially enterprise-affecting
- Are exploited in the wild or have exploits available
- Allow full system compromise
- Can be exploited via the network alone or in combination with other vulnerabilities
- Have a solution to take action on
In addition, all of these vulnerabilities are easily discoverable and therefore should be investigated and fixed immediately.
To proactively address these vulnerabilities and ensure comprehensive coverage beyond publicly available sources on an ongoing basis, organizations can leverage Flashpoint Vulnerability Intelligence. Flashpoint provides comprehensive coverage encompassing IT, OT, IoT, CoTs, and open-source libraries and dependencies. It catalogs over 100,000 vulnerabilities that are not included in the NVD or lack a CVE ID, ensuring thorough coverage beyond publicly available sources. The vulnerabilities that are not covered by the NVD do not yet have CVE ID assigned and will be noted with a VulnDB ID.
| CVE ID | Title | CVSS Scores (v2, v3, v4) | Exploit Status | Exploit Consequence | Ransomware Likelihood Score | Social Risk Score | Solution Availability |
| CVE-2025-33222 | NVIDIA Isaac Launchable Unspecified Hardcoded Credentials | 5.0 9.8 9.3 | Private | Credential Disclosure | High | Low | Yes |
| CVE-2025-33223 | NVIDIA Isaac Launchable Unspecified Improper Execution Privileges Remote Code Execution | 10.0 9.8 9.3 | Private | Remote Code Execution | High | Low | Yes |
| CVE-2025-68613 | n8n Package for Node.js packages/workflow/src/expression-evaluator-proxy.ts Workflow Expression Evaluation Remote Code Execution | 9.0 9.9 9.4 | Public | Remote Code Execution | High | High | Yes |
| CVE-2025-14847 | MongoDB transport/message_compressor_zlib.cpp ZlibMessageCompressor::decompressData() Function Zlib Compressed Protocol Header Handling Remote Uninitialized Memory Disclosure (Mongobleed) | 10.0 9.8 9.3 | Public | Uninitialized Memory Disclosure | High | High | Yes |
NOTES: The severity of a given vulnerability score can change whenever new information becomes available. Flashpoint maintains its vulnerability database with the most recent and relevant information available. Login to view more vulnerability metadata and for the most up-to-date information.
CVSS scores: Our analysts calculate, and if needed, adjust NVD’s original CVSS scores based on new information being available.
Social Risk Score: Flashpoint estimates how much attention a vulnerability receives on social media. Increased mentions and discussions elevate the Social Risk Score, indicating a higher likelihood of exploitation. The score considers factors like post volume and authors, and decreases as the vulnerability’s relevance diminishes.
Ransomware Likelihood: This score is a rating that estimates the similarity between a vulnerability and those known to be used in ransomware attacks. As we learn more information about a vulnerability (e.g. exploitation method, technology affected) and uncover additional vulnerabilities used in ransomware attacks, this rating can change.
Flashpoint Ignite lays all of these components out. Below is an example of what this vulnerability record for CVE-2025-33223 looks like.
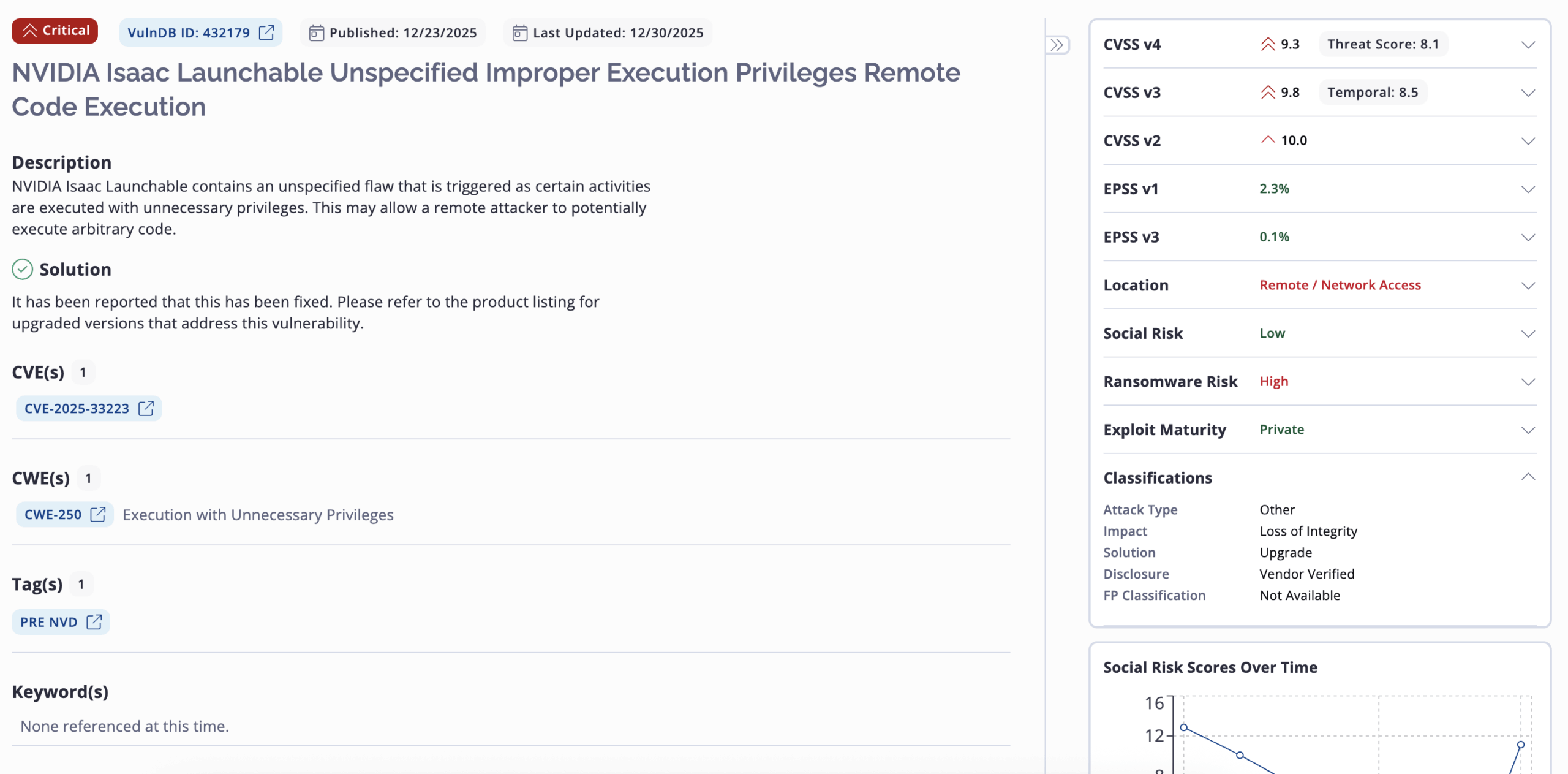
This record provides additional metadata like affected product versions, MITRE ATT&CK mapping, analyst notes, solution description, classifications, vulnerability timeline and exposure metrics, exploit references and more.
Analyst Comments on the Notable Vulnerabilities
Below, Flashpoint analysts describe the five vulnerabilities highlighted above as vulnerabilities that should be of focus for remediation if your organization is exposed.
CVE-2025-33222
NVIDIA Isaac Launchable contains a flaw that is triggered by the use of unspecified hardcoded credentials. This may allow a remote attacker to trivially gain privileged access to the program.
CVE-2025-33223
NVIDIA Isaac Launchable contains an unspecified flaw that is triggered as certain activities are executed with unnecessary privileges. This may allow a remote attacker to potentially execute arbitrary code.
CVE-2025-68613
n8n Package for Node.js contains a flaw in packages/workflow/src/expression-evaluator-proxy.ts that is triggered as workflow expressions are evaluated in an improperly isolated execution context. This may allow an authenticated, remote attacker to execute arbitrary code with the privileges of the n8n process.
CVE-2025-14847
MongoDB contains a flaw in the ZlibMessageCompressor::decompressData() function in mongo/transport/message_compressor_zlib.cpp that is triggered when handling mismatched length fields in Zlib compressed protocol headers. This may allow a remote attacker to disclose uninitialized memory contents on the heap.
Previously Highlighted Vulnerabilities
| CVE/VulnDB ID | Flashpoint Published Date |
| CVE-2025-21218 | Week of January 15, 2025 |
| CVE-2024-57811 | Week of January 15, 2025 |
| CVE-2024-55591 | Week of January 15, 2025 |
| CVE-2025-23006 | Week of January 22, 2025 |
| CVE-2025-20156 | Week of January 22, 2025 |
| CVE-2024-50664 | Week of January 22, 2025 |
| CVE-2025-24085 | Week of January 29, 2025 |
| CVE-2024-40890 | Week of January 29, 2025 |
| CVE-2024-40891 | Week of January 29, 2025 |
| VulnDB ID: 389414 | Week of January 29, 2025 |
| CVE-2025-25181 | Week of February 5, 2025 |
| CVE-2024-40890 | Week of February 5, 2025 |
| CVE-2024-40891 | Week of February 5, 2025 |
| CVE-2024-8266 | Week of February 12, 2025 |
| CVE-2025-0108 | Week of February 12, 2025 |
| CVE-2025-24472 | Week of February 12, 2025 |
| CVE-2025-21355 | Week of February 24, 2025 |
| CVE-2025-26613 | Week of February 24, 2025 |
| CVE-2024-13789 | Week of February 24, 2025 |
| CVE-2025-1539 | Week of February 24, 2025 |
| CVE-2025-27364 | Week of March 3, 2025 |
| CVE-2025-27140 | Week of March 3, 2025 |
| CVE-2025-27135 | Week of March 3, 2025 |
| CVE-2024-8420 | Week of March 3, 2025 |
| CVE-2024-56196 | Week of March 10, 2025 |
| CVE-2025-27554 | Week of March 10, 2025 |
| CVE-2025-22224 | Week of March 10, 2025 |
| CVE-2025-1393 | Week of March 10, 2025 |
| CVE-2025-24201 | Week of March 17, 2025 |
| CVE-2025-27363 | Week of March 17, 2025 |
| CVE-2025-2000 | Week of March 17, 2025 |
| CVE-2025-27636 CVE-2025-29891 | Week of March 17, 2025 |
| CVE-2025-1496 | Week of March 24, 2025 |
| CVE-2025-27781 | Week of March 24, 2025 |
| CVE-2025-29913 | Week of March 24, 2025 |
| CVE-2025-2746 | Week of March 24, 2025 |
| CVE-2025-29927 | Week of March 24, 2025 |
| CVE-2025-1974 CVE-2025-2787 | Week of March 31, 2025 |
| CVE-2025-30259 | Week of March 31, 2025 |
| CVE-2025-2783 | Week of March 31, 2025 |
| CVE-2025-30216 | Week of March 31, 2025 |
| CVE-2025-22457 | Week of April 2, 2025 |
| CVE-2025-2071 | Week of April 2, 2025 |
| CVE-2025-30356 | Week of April 2, 2025 |
| CVE-2025-3015 | Week of April 2, 2025 |
| CVE-2025-31129 | Week of April 2, 2025 |
| CVE-2025-3248 | Week of April 7, 2025 |
| CVE-2025-27797 | Week of April 7, 2025 |
| CVE-2025-27690 | Week of April 7, 2025 |
| CVE-2025-32375 | Week of April 7, 2025 |
| VulnDB ID: 398725 | Week of April 7, 2025 |
| CVE-2025-32433 | Week of April 12, 2025 |
| CVE-2025-1980 | Week of April 12, 2025 |
| CVE-2025-32068 | Week of April 12, 2025 |
| CVE-2025-31201 | Week of April 12, 2025 |
| CVE-2025-3495 | Week of April 12, 2025 |
| CVE-2025-31324 | Week of April 17, 2025 |
| CVE-2025-42599 | Week of April 17, 2025 |
| CVE-2025-32445 | Week of April 17, 2025 |
| VulnDB ID: 400516 | Week of April 17, 2025 |
| CVE-2025-22372 | Week of April 17, 2025 |
| CVE-2025-32432 | Week of April 29, 2025 |
| CVE-2025-24522 | Week of April 29, 2025 |
| CVE-2025-46348 | Week of April 29, 2025 |
| CVE-2025-43858 | Week of April 29, 2025 |
| CVE-2025-32444 | Week of April 29, 2025 |
| CVE-2025-20188 | Week of May 3, 2025 |
| CVE-2025-29972 | Week of May 3, 2025 |
| CVE-2025-32819 | Week of May 3, 2025 |
| CVE-2025-27007 | Week of May 3, 2025 |
| VulnDB ID: 402907 | Week of May 3, 2025 |
| VulnDB ID: 405228 | Week of May 17, 2025 |
| CVE-2025-47277 | Week of May 17, 2025 |
| CVE-2025-34027 | Week of May 17, 2025 |
| CVE-2025-47646 | Week of May 17, 2025 |
| VulnDB ID: 405269 | Week of May 17, 2025 |
| VulnDB ID: 406046 | Week of May 19, 2025 |
| CVE-2025-48926 | Week of May 19, 2025 |
| CVE-2025-47282 | Week of May 19, 2025 |
| CVE-2025-48054 | Week of May 19, 2025 |
| CVE-2025-41651 | Week of May 19, 2025 |
| CVE-2025-20289 | Week of June 3, 2025 |
| CVE-2025-5597 | Week of June 3, 2025 |
| CVE-2025-20674 | Week of June 3, 2025 |
| CVE-2025-5622 | Week of June 3, 2025 |
| CVE-2025-5419 | Week of June 3, 2025 |
| CVE-2025-33053 | Week of June 7, 2025 |
| CVE-2025-5353 | Week of June 7, 2025 |
| CVE-2025-22455 | Week of June 7, 2025 |
| CVE-2025-43200 | Week of June 7, 2025 |
| CVE-2025-27819 | Week of June 7, 2025 |
| CVE-2025-49132 | Week of June 13, 2025 |
| CVE-2025-49136 | Week of June 13, 2025 |
| CVE-2025-50201 | Week of June 13, 2025 |
| CVE-2025-49125 | Week of June 13, 2025 |
| CVE-2025-24288 | Week of June 13, 2025 |
| CVE-2025-6543 | Week of June 21, 2025 |
| CVE-2025-3699 | Week of June 21, 2025 |
| CVE-2025-34046 | Week of June 21, 2025 |
| CVE-2025-34036 | Week of June 21, 2025 |
| CVE-2025-34044 | Week of June 21, 2025 |
| CVE-2025-7503 | Week of July 12, 2025 |
| CVE-2025-6558 | Week of July 12, 2025 |
| VulnDB ID: 411705 | Week of July 12, 2025 |
| VulnDB ID: 411704 | Week of July 12, 2025 |
| CVE-2025-6222 | Week of July 12, 2025 |
| CVE-2025-54309 | Week of July 18, 2025 |
| CVE-2025-53771 | Week of July 18, 2025 |
| CVE-2025-53770 | Week of July 18, 2025 |
| CVE-2025-54122 | Week of July 18, 2025 |
| CVE-2025-52166 | Week of July 18, 2025 |
| CVE-2025-53942 | Week of July 25, 2025 |
| CVE-2025-46811 | Week of July 25, 2025 |
| CVE-2025-52452 | Week of July 25, 2025 |
| CVE-2025-41680 | Week of July 25, 2025 |
| CVE-2025-34143 | Week of July 25, 2025 |
| CVE-2025-50454 | Week of August 1, 2025 |
| CVE-2025-8875 | Week of August 1, 2025 |
| CVE-2025-8876 | Week of August 1, 2025 |
| CVE-2025-55150 | Week of August 1, 2025 |
| CVE-2025-25256 | Week of August 1, 2025 |
| CVE-2025-43300 | Week of August 16, 2025 |
| CVE-2025-34153 | Week of August 16, 2025 |
| CVE-2025-48148 | Week of August 16, 2025 |
| VulnDB ID: 416058 | Week of August 16, 2025 |
| CVE-2025-32992 | Week of August 16, 2025 |
| CVE-2025-7775 | Week of August 24, 2025 |
| CVE-2025-8424 | Week of August 24, 2025 |
| CVE-2025-34159 | Week of August 24, 2025 |
| CVE-2025-57819 | Week of August 24, 2025 |
| CVE-2025-7426 | Week of August 24, 2025 |
| CVE-2025-58367 | Week of September 1, 2025 |
| CVE-2025-58159 | Week of September 1, 2025 |
| CVE-2025-58048 | Week of September 1, 2025 |
| CVE-2025-39247 | Week of September 1, 2025 |
| CVE-2025-8857 | Week of September 1, 2025 |
| CVE-2025-58321 | Week of September 8, 2025 |
| CVE-2025-58366 | Week of September 8, 2025 |
| CVE-2025-58371 | Week of September 8, 2025 |
| CVE-2025-55728 | Week of September 8, 2025 |
| CVE-2025-55190 | Week of September 8, 2025 |
| VulnDB ID: 419253 | Week of September 13, 2025 |
| CVE-2025-10035 | Week of September 13, 2025 |
| CVE-2025-59346 | Week of September 13, 2025 |
| CVE-2025-55727 | Week of September 13, 2025 |
| CVE-2025-10159 | Week of September 13, 2025 |
| CVE-2025-20363 | Week of September 20, 2025 |
| CVE-2025-20333 | Week of September 20, 2025 |
| CVE-2022-4980 | Week of September 20, 2025 |
| VulnDB ID: 420451 | Week of September 20, 2025 |
| CVE-2025-9900 | Week of September 20, 2025 |
| CVE-2025-52906 | Week of September 27, 2025 |
| CVE-2025-51495 | Week of September 27, 2025 |
| CVE-2025-27224 | Week of September 27, 2025 |
| CVE-2025-27223 | Week of September 27, 2025 |
| CVE-2025-54875 | Week of September 27, 2025 |
| CVE-2025-41244 | Week of September 27, 2025 |
| CVE-2025-61928 | Week of October 6, 2025 |
| CVE-2025-61882 | Week of October 6, 2025 |
| CVE-2025-49844 | Week of October 6 2025 |
| CVE-2025-57870 | Week of October 6, 2025 |
| CVE-2025-34224 | Week of October 6, 2025 |
| CVE-2025-34222 | Week of October 6, 2025 |
| CVE-2025-40765 | Week of October 11, 2025 |
| CVE-2025-59230 | Week of October 11, 2025 |
| CVE-2025-24990 | Week of October 11, 2025 |
| CVE-2025-61884 | Week of October 11, 2025 |
| CVE-2025-41430 | Week of October 11, 2025 |
| VulnDB ID: 424051 | Week of October 18, 2025 |
| CVE-2025-62645 | Week of October 18, 2025 |
| CVE-2025-61932 | Week of October 18, 2025 |
| CVE-2025-59503 | Week of October 18, 2025 |
| CVE-2025-43995 | Week of October 18, 2025 |
| CVE-2025-62168 | Week of October 18, 2025 |
| VulnDB ID: 425182 | Week of October 25, 2025 |
| CVE-2025-62713 | Week of October 25, 2025 |
| CVE-2025-54964 | Week of October 25, 2025 |
| CVE-2024-58274 | Week of October 25, 2025 |
| CVE-2025-41723 | Week of October 25, 2025 |
| CVE-2025-20354 | Week of November 1, 2025 |
| CVE-2025-11953 | Week of November 1, 2025 |
| CVE-2025-60854 | Week of November 1, 2025 |
| CVE-2025-64095 | Week of November 1, 2025 |
| CVE-2025-11833 | Week of November 1, 2025 |
| CVE-2025-64446 | Week of November 8, 2025 |
| CVE-2025-36250 | Week of November 8, 2025 |
| CVE-2025-64400 | Week of November 8, 2025 |
| CVE-2025-12686 | Week of November 8, 2025 |
| CVE-2025-59118 | Week of November 8, 2025 |
| VulnDB ID: 426231 | Week of November 8, 2025 |
| VulnDB ID: 427979 | Week of November 22, 2025 |
| CVE-2025-55796 | Week of November 22, 2025 |
| CVE-2025-64428 | Week of November 22, 2025 |
| CVE-2025-62703 | Week of November 22, 2025 |
| VulnDB ID: 428193 | Week of November 22, 2025 |
| CVE-2025-65018 | Week of November 22, 2025 |
| CVE-2025-54347 | Week of November 22, 2025 |
| CVE-2025-55182 | Week of November 29, 2025 |
| CVE-2024-14007 | Week of November 29, 2025 |
| CVE-2025-66399 | Week of November 29, 2025 |
| CVE-2022-35420 | Week of November 29, 2025 |
| CVE-2025-66516 | Week of November 29, 2025 |
| CVE-2025-59366 | Week of November 29, 2025 |
| CVE-2025-14174 | Week of December 6, 2026 |
| CVE-2025-43529 | Week of December 6, 2026 |
| CVE-2025-8110 | Week of December 6, 2026 |
| CVE-2025-59719 | Week of December 6, 2026 |
| CVE-2025-59718 | Week of December 6, 2026 |
| CVE-2025-14087 | Week of December 6, 2026 |
| CVE-2025-62221 | Week of December 6, 2026 |
Transform Vulnerability Management with Flashpoint
Request a demo today to see how Flashpoint can transform your vulnerability intelligence, vulnerability management, and exposure identification program.



