We are currently seeing an Oracle WebLogic vulnerability getting some attention as exploit code was published by multiple sources. Oracle provided patches on January 17, 2023 with the latest Critical Patch Update. Now that exploit code is publicly available it is time to ensure that those patches have been applied.
Looking at available code on Github and a write-up by RiverSec Lab, the exploit targets the Listen Port for the Administration Server (TCP/7001). The protocol used with this port is T3—Oracle’s proprietary Remote Method Invocation (RMI) protocol.
The Oracle WebLogic vulnerability is triggered when binding an instance of the ‘weblogic.deployment.jms.ForeignOpaqueReference’ class to a named object on the WebLogic Server. Via the ‘remoteJNDIName’ field, a JNDI lookup via the LDAP protocol to an attacker-controlled server can be triggered. Using the same technique as in the Log4Shell exploits, the attacker is able to achieve remote code execution.
One product, two CVEs, and three different impacts
We’ve noticed that some sources refer to this vulnerability as CVE-2023-21838, while others refer to it as CVE-2023-21839. Both CVEs seem related to the ‘ForeignOpaqueReference’ class. Interestingly, Oracle assigned neither of those two CVEs a CVSS score that reflects remote code execution on their Middleware Risk Matrix.
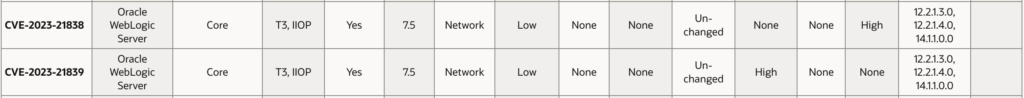
Oracle has classified CVE-2023-21838 as a remote denial-of-service and CVE-2023-21839 as a remote information disclosure, while the available exploit potentially allows remote code execution. ZDI, who reported CVE-2023-21838, did, however, report an impact that matches this.
In this case, it is difficult to figure out where an error in the classification occurred. Are there two remote code execution vulnerabilities? Has Oracle incorrectly assigned the CVSS score for one or both of them? At this point it isn’t clear, but this is a situation that our analysts will continue to monitor.
However, with the exploit code now publicly available, it is safe to say that Oracle WebLogic servers with exposed administration server ports will see an increase in exploits attempts.
The potential systemic and widespread impact
History often repeats itself, and we’ve seen these kinds of vulnerabilities have a systemic and widespread impact. Back in 2018, our research on Click2gov showed that numerous municipalities had been targeted and suffered data breaches—the culprit being an unpatched Weblogic vulnerability. Although many of the vulnerable municipalities did patch, the process was extremely slow and actually led to numerous data breaches. Let us hope previously affected organizations will be on top of these new issues.
Patch more effectively with Flashpoint
Sign up for a free trial and see how quality intelligence empowers a vulnerability risk management program, allowing your security teams to prioritize and remediate what really matters.


