June 2023
While most security vendors mainly focus on Microsoft releases on Patch Tuesday, our Flashpoint VulnDB team closely tracks and covers all releases by participating vendors, all while pushing standardized alerts to our clients. For June’s Patch Tuesday event, our team covered a total of 231 new vulnerabilities and updated 682 VulnDB entries with additional information with the remaining lower severity issues being covered Wednesday. A hard day for vulnerability management teams.
The first vendor of the day to release their security fixes was SAP with 7 new vulnerabilities. Two of these vulnerabilities received a “High” severity rating. One was an authenticated stored cross-site scripting vulnerability in UI5 Variant Management, CVE-2023-33991, while the other, CVE-2023-2827, allowed sending unauthorized service requests to SAP Plant Connectivity or Production Connector for SAP Digital Manufacturing due to missing JSON Web Token validation.
The next vendor to follow was Siemens with 15 new vulnerabilities along with many updates to existing issues.
CVE-2023-25910 has been assigned for a vulnerability in SIMATIC STEP 7 and derived products. Embedded functions in the included database management system could be used to inject and execute arbitrary code on the server.
Siemens JT2Go and Teamcenter Visualization also received security updates this month. CVE-2023-33124 covers a memory corruption vulnerability that may allow code execution when parsing specially crafted CGM files. As Siemens regularly addresses vulnerabilities that can be triggered via malicious files in these products extra care should be taken whenever considering opening untrusted files using this application.
Within the batch of Siemens updates, CVE-2023-29129 represents an incomplete fix for CVE-2023-25957. This update addresses an incomplete fix for a remote authentication bypass in Siemens Mendix due to insufficient verification of SAML assertions in a specific non-default configuration.
Later in the day, we saw releases from Synology (2 new vulnerabilities), Rockwell Automation (4 new vulnerabilities), Citrix (1 new vulnerability), Schneider Electric (4 new vulnerabilities), VMWare (1 new vulnerability), and Apache Traffic Server (3 new vulnerabilities) before the two main vendors of the day, Adobe and Microsoft, finally released their security advisories covering 18 and 70 new vulnerabilities (94 including updates), respectively.
The curious case of Zoom Video Communications
Another vendor that also released security bulletins during Patch Tuesday was Zoom Video Communications. While the vendor’s security page lists 12 new vulnerabilities, it seems they had some problems, as many of these vulnerabilities were already available in a Google cached version of the vendor’s security page prior to Patch Tuesday. This made it possible for Flashpoint to publish information about the majority of these vulnerabilities to VulnDB customers before they were officially listed on Zoom’s security page.
Google Pixel surprise release
A vendor that made a surprise appearance for Patch Tuesday was Google. Not only did Google release fixes for 5 vulnerabilities in Chrome, but they also published a security bulletin for Google Pixel covering 74 new vulnerabilities. Usually, Google Pixel bulletins are released at the same time as the Android security bulletins i.e. the beginning of the month. For unknown reasons that didn’t happen this month with it instead releasing in the middle of Patch Tuesday.
One of the issues addressed in Google Chrome, CVE-2023-3214, was in the Autofill payments functionality and rated “Critical”. Per Google, vulnerabilities rated “Critical” in Google Chrome generally aren’t restricted by the sandbox and “allow an attacker to read or write arbitrary resources (including but not limited to the file system, registry, network, etc.) on the underlying platform, with the user’s full privileges.”
Three of the fixed vulnerabilities are in the Chrome browser with the remaining two in the WebRTC and V8 libraries. Unlike a recent report of a Google V8 zero-day, there are no reports of any of these vulnerabilities being actively exploited.
The same is not true for the vulnerabilities reported in the Google Pixel security bulletin. For CVE-2023-21237, there are indications that it “may be under limited, targeted exploitation.” While no details are publicly available, the issue seems to be related to a problem handling custom notifications that are not required to have a minimum height.
Microsoft vulnerabilities worth mentioning
Microsoft did not fix any zero-day vulnerabilities this month. However, the vendor still addressed some vulnerabilities that are worth mentioning:
Microsoft Exchange Server Remote Code Execution Vulnerabilities
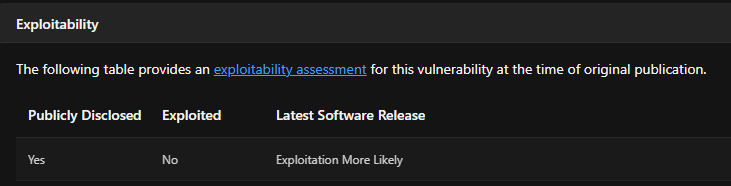
Two of the vulnerabilities fixed by Microsoft this month, CVE-2023-28310 and CVE-2023-32031, are in Microsoft Exchange server and could be exploited for remote code execution by authenticated attackers with low privileges. Microsoft rates both vulnerabilities as “Exploitation More Likely”, which means that “Microsoft analysis has shown that exploit code could be created in such a way that an attacker could consistently exploit this vulnerability.”
Microsoft SharePoint Server Elevation of Privilege Vulnerability
A vulnerability in Microsoft SharePoint Server 2019, CVE-2023-29357, could allow an unauthenticated remote attacker to bypass authentication via spoofed JWT authentication tokens and potentially gain administrator privileges. While exploitation has not been proven, Microsoft rates this vulnerability as “Exploitation More Likely”.
Microsoft does mention as a mitigating factor that “Customers who have enabled the AMSI integration feature and use Microsoft Defender across their SharePoint Server farm(s) are protected from this vulnerability.”
Multiple Privilege Escalation Vulnerabilities
Microsoft also fixed five local privilege escalation vulnerabilities in Windows, CVE-2023-29358, CVE-2023-29359, CVE-2023-29371, CVE-2023-29360, and CVE-2023-29361, that affect the Graphics Device Interface (GDI) component, TPM device driver, and Cloud Files mini filter driver. These vulnerabilities may allow a local attacker to gain SYSTEM privileges. While exploitation has not been proven for any of these five vulnerabilities, Microsoft classifies all of them as “Exploitation More Likely”. It should be noted that although these have a local attack vector, these types of vulnerabilities are often exploited as the last part of an exploit chain that first somehow compromises a system and then utilizes the local privilege escalation vulnerability to gain full control over the compromised system.
Microsoft did address other vulnerabilities with higher CVSS scores, but these were all rated as “Exploitation Less Likely”. This should not be viewed as a guarantee that exploits for these vulnerabilities won’t surface, so if these products are used for critical assets they should still be prioritized.
Other vulnerabilities worth mentioning
CVE-2023-20867: VMware released an update for VMware Tools that addresses an authentication bypass in the vgauth module. An attacker with privileged access to an ESXi host can send guest operation requests to a guest virtual machine without prior authentication.This allows executing privileged commands and file transfers in the VM without generating an authentication log event. Mandiant has provided further details that this issue has been discovered as a zero-day and exploited by the UNC3886 group.
CVE-2023-24489: Citrix has reported that a customer-managed Citrix ShareFile StorageZones Controller may be susceptible to “remote compromise”. Only limited details have been provided, but the issue is related to improper access control for an unspecified resource. While “compromise” is not further specified, this vulnerability is worth mentioning as the provided CVSSv3.1 vector string indicates that the vendor is aware of a fully functional exploit.
Over the next few days we expect to add a lot of new details to many of these entries both based on external research and research performed by our in-house team.
May 2023
Yesterday was the monthly (in)famous Patch Tuesday, where many major vendors release vulnerability fixes for their products. While many vendors mainly focus on the Microsoft releases, our Flashpoint VulnDB team, as usual, closely tracked and covered the releases by all the different vendors and pushed standardized alerts to our clients. A total of 220 new vulnerabilities were covered by the team and another 562 VulnDB entries were updated with additional information with the remaining lower severity issues being covered Wednesday.
The first vendor of the day to release their security fixes was SAP with 15 new vulnerabilities. None of those stood out as critical with the most severe being CVE-2023-32111, which could lead to a remote denial of service in SAP PowerDesigner Proxy. System administrators of SAP systems should still evaluate the fixed issues and determine the impact to their specific environment and how to prioritize the patch effort.
The next vendor to follow was Siemens, who also released a total of 15 new vulnerabilities along with a lot of updates to existing issues. Three vulnerabilities stood out from the rest: two vulnerabilities in the Siemens Siveillance Video product that could lead to authenticated remote code execution (CVE-2023-30898 and CVE-2023-30899) as well as an authenticated remote command injection vulnerability in the Siemens SCALANCE LPE9403 product (CVE-2023-27407).
Later in the day, we saw releases from Mozilla (31 new vulnerabilities), Rockwell Automation (3 new vulnerabilities), Citrix (2 new vulnerabilities), Schneider Electric (2 new vulnerabilities), AMD (26 new vulnerabilities), and Intel (85 new vulnerabilities) before the two main vendors of the day, Adobe and Microsoft, finally released their security advisories covering 14 and 38 new vulnerabilities (49 including updates), respectively.
The vulnerabilities fixed by Adobe this month only affected Adobe Substance 3D Painter. If using this product, be aware that some of these fixes did address potential code execution vulnerabilities so applying the update should be prioritized.
Of the remaining vulnerabilities addressed by this Patch Tuesday, the two that mostly stood out were two 0-days fixed by Microsoft: CVE-2023-29336 and CVE-2023-24932. Please note that some media and security vendors claim that Microsoft addressed three 0-day vulnerabilities by erroneously including CVE-2023-29325 in the mix.
Two Microsoft 0-days
Secure Boot Security Feature Bypass Vulnerability
The first 0-day addressed by Microsoft is CVE-2023-24932, which is a local vulnerability in the boot manager that allows bypassing the Secure Boot protection mechanism. According to Microsoft, this is actively being exploited “by the BlackLotus bootkit to exploit CVE-2022-21894.” It should be noted that in order to exploit this vulnerability, an attacker would either need physical access or administrative rights to the system. The most plausible attack vector would not be a malicious Administrator but rather malicious code planted on the system via exploitation of another vulnerability or vulnerability chain that allowed compromising the system and gaining administrative rights.
While a patch is available to address this vulnerability it’s imperative that people note that after applying the fix, additional actions are required to fully implement the protections. Microsoft also warns that “if this fix is not properly enabled there is a potential to cause disruption and prevent a system from starting up.” Details are available in the accompanying guidance document provided by Microsoft.
Microsoft state that they will be providing a second release on 2023/07/11 to “provide additional update options to simplify the deployment of the protections.” Finally, Microsoft plans to release a final version of the fix during the first quarter 2024 to “enable the fix for CVE-2023-24932 by default and enforce bootmanager revocations on all Windows devices.”
Win32k Elevation of Privilege Vulnerability
The second 0-day addressed by Microsoft is CVE-2023-29336. This is a local privilege escalation vulnerability within the Win32k component that allows gaining SYSTEM privileges. No details are currently available about the scope of active exploitation or targets. Our team is actively monitoring this vulnerability as well as researching more details.
Other vulnerabilities worth mentioning
Apart from the two 0-days, based on the vague currently available information about the vulnerabilities fixed, the following stand out as being worth keeping an eye on and address in a timely manner:
CVE-2023-29325
As previously mentioned, this is the vulnerability that some sources incorrectly refer to as a 0-day. It is not. Microsoft’s security bulletin lists it as “Publicly Disclosed: Yes” but “Exploited: No”.
This means that details about the vulnerability were shared publicly prior to the security bulletin being released i.e. an uncoordinated disclosure, but not that it was actively exploited as a zero-day. Microsoft does, however, flag it as “Exploitation More Likely” so it’s one of the vulnerabilities that should be prioritized to address. The issue was reported to Microsoft by Will Dormann, who shared further information about his findings:
Apparently, simply referencing two CLSIDs ({00000315-0000-0000-C000-000000000046} or {00000316-0000-0000-C000-000000000046}) as a COM object in a Rich Text email would crash Outlook. Upon further investigation, Microsoft determined that this has a potential code execution impact and can even be triggered from the Preview Pane. As a workaround, Microsoft recommends reading email in plain text format.
CVE-2023-24902
This is another privilege escalation vulnerability in the Win32k component. While this is not currently being actively exploited unlike CVE-2023-29336, Microsoft does rate it as “Exploitation More Likely”. Similar to the actively exploited vulnerability this could allow local attackers to gain SYSTEM privileges.
CVE-2023-24954
This is an information disclosure vulnerability in Microsoft SharePoint Server. While authentication is required, Microsoft states that it could be exploited to disclose “user tokens and other potentially sensitive information.” This vulnerability is also rated by Microsoft as “Exploitation More Likely”.
CVE-2023-24941
The final vulnerability worth prioritizing is in the Network File System (NFS) service and can potentially be exploited for remote code execution via a specially crafted request. Microsoft clarifies that NFSV2.0 and NFSV3.0 are not affected. Exploitation is also deemed more likely for this vulnerability.
Microsoft did address other vulnerabilities with higher CVSS scores e.g. in the Bluetooth driver, LDAP functionality, Microsoft Office, SSTP (Secure Socket Tunneling Protocol), PGM (Pragmatic General Multicast) feature, and AV1 video extension. However, these were all rated as “Exploitation Less Likely”. This should not be viewed as a guarantee that exploits for these vulnerabilities won’t surface, so these would still be prudent to also prioritize.
Over the next few days we expect to add a lot of new details to many of these entries both based on external research and research performed by our in-house team.


